10 Cyber Security Engineering Interview Questions and Answers (+ Interview Tips)
Learn 10 frequently asked cyber security interview questions and answers and how to prepare for a cyber security engineer interview.
Organizations with any type of computer system or software need strong information security practices to protect their data from breaches. A cyber security engineer’s job is to find any security risks and address them.
Maybe you’re applying for cyber security engineer jobs or looking to add one to your team. Below, learn more about cyber security engineers and 10 of the most common cyber security engineer interview questions.
- What is the role of a cyber security engineer?
- The top 7 skills required for cyber security jobs
- Top 10 frequently asked cyber security interview questions and answers
- How to prepare for a cyber security engineer interview
What is the role of a cyber security engineer?
A cyber security engineer is responsible for identifying threats and security compromises in an organization’s software, data, networks, and computer systems. They create solutions that protect against cyber attacks such as malware, brute force attacks, and ransomware.

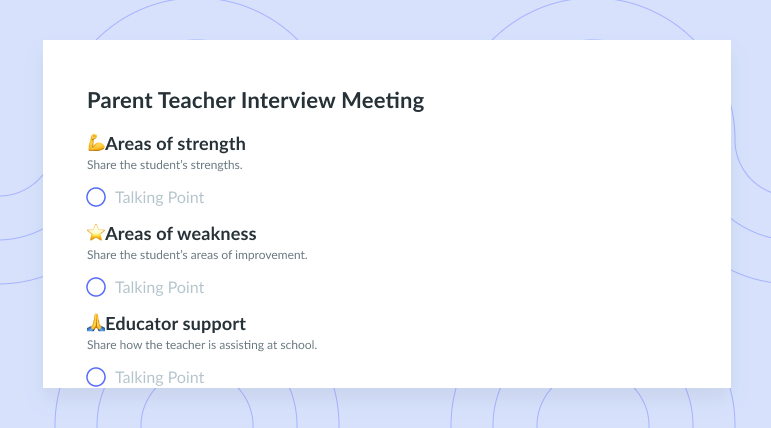
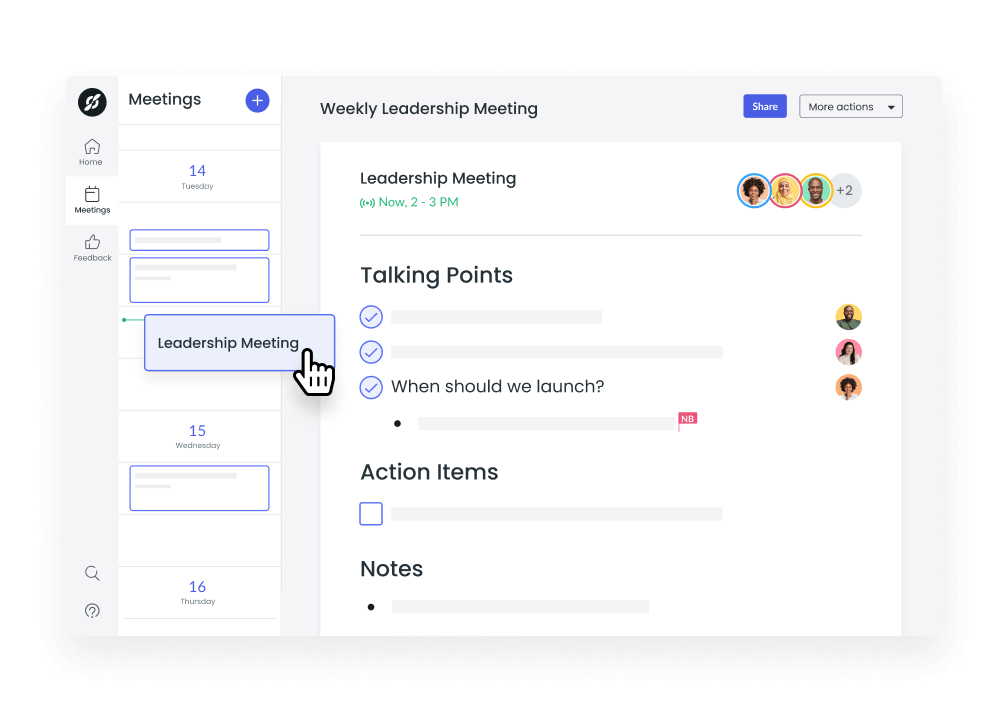
Build a culture of effective meetings with your engineering team
Level up your engineering meeting habits to boost engagement and productivity with a collaborative meeting agenda. Try a tool like Fellow!
The top 7 skills required for cyber security jobs
There are several skills cyber security engineers should know to do well in their roles. Below are seven of the most important skills for cybersecurity engineers.
- Problem-solving
- Technical aptitude
- Experience with many platforms
- Attention to detail
- Communication
- Computer forensics
- Familiarity with hacking tactics
1Problem-solving
A cyber security engineer is in charge of identifying and solving network security issues within their organization’s systems. When they find issues, these engineers need critical thinking and problem skills to troubleshoot and arrive at solutions.
2Technical aptitude
Cybersecurity professionals need a strong understanding of the most intricate and technical parts of the networks, hardware and software systems, and digital platforms they oversee. Knowledge of programming languages such as Java, Javascript, and SQL, or using different networks like VPN are essential to managing databases and keeping security protocols up to date.
3Experience with many platforms
Many organizations have programs that run on mobile, desktop, and cloud platforms. This means their cyber security engineers need a thorough understanding of how all these platforms work. They also need comprehensive mobile and web development knowledge so they can maintain these platforms’ security.
4Attention to detail
To identify issues with their hardware, software, and computer systems, cybersecurity engineers need an eye for detail. This attention to detail is also important for creating solutions that directly and effectively address any issues.
5Communication
Cybersecurity engineers must have clear communication skills, both written and verbal. When issues arise, these engineers need to draft reports that outline the problem and their plan of action. They must also communicate effectively with their team members to guide them through the steps and procedures involved in reaching a solution.
6Computer forensics
Computer forensics is a field that involves tracking and investigating digital information stored on a device. Cybersecurity engineers need to be well versed in it so they can better find and seal the data leakages that cyber attacks cause.
7Familiarity with hacking tactics
You’ve probably heard the saying, “It takes one to know one.” While cyber security engineers aren’t hackers, they can be seen, in a way, as ethical hackers (a.k.a. “white hat hackers”). When they understand common hacking tactics, strategies, and are familiar with trends and phishing statistics they can better fight off threat actors. Ethical hacking is thus a great foundation for getting ahead of potential security issues and creating the right defenses.
Top 10 frequently asked cyber security interview questions and answers
There are some common questions that managers ask when interviewing candidates for a cybersecurity position. Below are 10 questions that interviewers commonly ask.
- What is cyber security?
- What is the difference between IDS and IPS?
- What is a botnet?
- What is the difference between stored and reflected XSS?
- What are HTTP response codes?
- What are the common types of cybersecurity attacks?
- What is a cyber security risk assessment?
- What is patch management?
- Which is more secure: SSL or HTTPS?
- How do you protect data in transit vs. rest?
1What is cyber security?
Why it’s asked: This question helps interviewers see whether a candidate knows the basics of cybersecurity. It shows whether the candidate is fairly new to the field or has been in it for a good long while.
The answer: Cybersecurity is the practice of protecting computers, systems, networks, mobile devices, and data from hackers and other security threats. Also known as IT security, cybersecurity protects an organization’s systems from both external and internal attacks.
2What is the difference between IDS and IPS?
Why it’s asked: An interviewer might ask this question to see whether a candidate knows the systems designed to identify and monitor vulnerabilities.
The answer: An intrusive detection system (IDS) tracks a network’s events and assesses them to find security vulnerabilities or threats. An intrusion prevention system (IPS) does the same while responding to any breaches.
3What is a botnet?
Why it’s asked: Cybersecurity engineers need to understand the potential effects of a cyber attack. Botnets are a key issue that can arise, so cybersecurity engineers should know what they are and how to solve the problem.
The answer: Short for “robot network,” a botnet is a group of computers infected with malware. These computers are connected over the network, and bots control them through a remote hacker. This hacker can use the botnet to force the network to follow certain instructions at any time.
4What is the difference between stored and reflected XSS?
Why it’s asked: Interviewers might want to know that a candidate understands the difference between these two security vulnerabilities. This can lead to further discussion about how an engineer would address these issues.
The answer: Stored cross-site scripting (XSS) happens when a malicious script is stored directly on a web application. This means all someone has to do is visit the webpage in question to see the attack. Reflected cross-site scripting, on the other hand, may require someone to click a link to see the breach.
5What are HTTP response codes?
Why it’s asked: Interviewers want to be sure that candidates know how to see and understand any problems with a website loading.
The answer: HTTP response codes are key to sharing information about whether browsers and servers are communicating well. They represent the status of an HTTP request to a server. There are five classes of response codes: informational, successful, redirection, client error, and server error.
6What are the common types of cybersecurity attacks?
Why it’s asked: Interviewers want to feel certain a candidate knows the types of attacks to look for and how they can affect the organization.
The answer: There are several types of cyber attacks. These include man-in-the-middle attacks, phishing, malware, rogue software, DDoS attacks, SQL injections, and password attacks.
7What is a cyber security risk assessment?
Why it’s asked: Knowing how to run a risk assessment is key to finding threats to a network before an actual attack happens.
The answer: A cyber security risk assessment is the process of figuring out and assessing a network’s risk of vulnerabilities and threats. This type of assessment can help an organization stay ahead of cyber threats and reduce the chances of an attack.
8What is patch management?
Why it’s asked: Patch management is key to rolling out updates and knowing how these changes could affect a network.
The answer: Patch management is the process of updating software or changing its code. It helps keep networks and systems up to date, which is great for security.
9Which is more secure: SSL or HTTPS?
Why it’s asked: Cybersecurity engineers need to understand the security differences between these key internet protocols.
The answer: SSL is more secure than HTTPS.
10How do you protect data in transit vs. rest?
Why it’s asked: Understanding the differences between these types of data can help cybersecurity engineers figure out the best ways to encrypt them.
The answer: Data in transit is information moving from one place to another. Data at rest is information stored in one place. Certain solutions such as firewalls, network access controls, and antivirus software can protect them both.
How to prepare for a cyber security engineer interview
Engineering leaders can use the questions above and some tips on how to interview engineers to find the right new team members. If you’re instead looking to work as a cybersecurity engineer, below are some tips that can help you get ready for your interview.
- Make sure your resume is well done
- Research the company
- Ask for a mock interview with at least two different people
- Take notes to show you’re engaged by
- Be ready for an onslaught of interviewers
- Be ready for any type of interview
- Write down the names of the people interviewing you
- Ask a question or two at the end
- Thank them at the end – and follow up with a thank-you email
1Make sure your resume is well done
Your resume is an organization’s first impression of you. To put your best foot forward, update your resume to show your most recent relevant experience. Carefully review your resume once, twice, and again to make sure you don’t have any typos. After all, being thorough is a big part of any cybersecurity engineering job.
2Research the company
Researching an employer before your interview can help you come off super prepared and interested during your interview. You should ask your interviewer some in-depth questions that reflect how much research you’ve done. Here’s a great example: “I noticed that you all made some updates to your software systems recently. What types of encryption protocols did you follow?”
3Ask for a mock interview with at least two different people
Practice makes perfect. Get a friend, colleague, mentor, or cybersecurity engineer whom you know to hold a mock interview for you. This way, you can naturally go over the talking points you want to raise during the real interview. Your mock interviewees should ask you some of the questions above to help you prepare your answers so you can ace them during the interview.
4Take notes to show you’re engaged by
During your interview, you might hear all kinds of information. Chances are, you’re not going to remember it all. So take notes about it all, especially the answers to any questions you ask. This way, you can show that you’re engaged and interested during the interview – and have everything you need to follow up later.
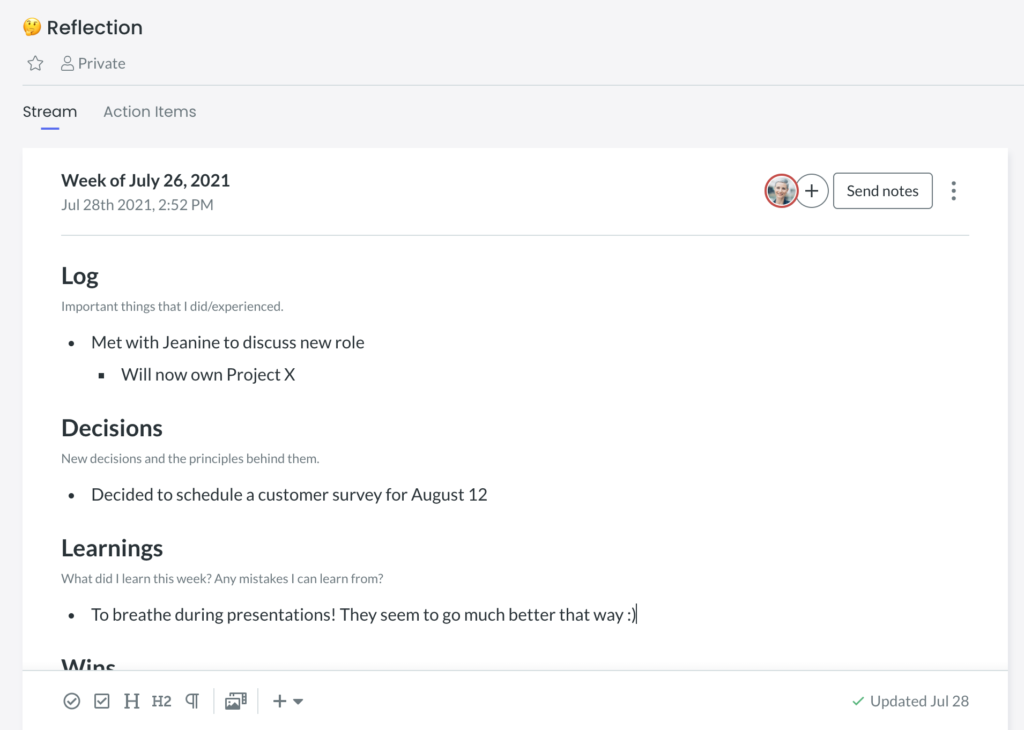
With Fellow, you can take interview notes in your private Streams, a digital notepad to track all of your thoughts in one place.
5Be ready for an onslaught of interviewers
It’s pretty common for cyber security engineer candidates to go through three to five rounds of interviews before hearing a decision. IT managers want to be sure their new cybersecurity team member really has what it takes to help keep everything secure and running properly. Think of each of these interviews as a new chance to show off your knowledge, skills, and qualifications.
6Be ready for any type of interview
You might have a group interview one day and a more hands-on interview another day. Either way, try to be ready for any type of interview a hiring manager might plan. This way, you can feel confident walking into the interview no matter what. And when you feel more confident, you’ll likely come off as a better candidate.
7Write down the names of the people interviewing you
Jot down the names of the people interviewing you so that you have an easy point of contact as you move through your interviews. Ask the interviewers to confirm their last names’ spelling if you’re not sure of it. You’ll probably need this later.
8Ask a question or two at the end
To really show that you’ve been engaged throughout the interview, try to ask a couple at the end. Make sure to ask questions that give you further insight into the work you’ll be doing. For example, “What’s the most important thing you would need me to achieve in my first 90 days?” You might also ask, “What are some of the first projects I’ll be taking on when I start?”
9Thank them at the end – and follow up with a thank-you email
Once your interview has wrapped up, thank your interviewees for taking the time to sit down with you and consider you. Then, remember when you got the names of the people who interviewed you? It’s time to include them in a thank-you email.
No more than 24 hours after your interview, write up an email expressing your gratitude once again. Show that you’re grateful for the opportunity to learn more about the open position and present yourself as a qualified candidate. Hiring managers often appreciate the gesture and may only consider candidates who take this extra step.
Providing optimal security
Cybersecurity engineers provide the best security standards and protocols for their organization’s networks. With their variety of soft and hard skills, these specialists are often highly valued IT team members.
If you’re an engineering leader within your organization, you can use Fellow to hold great one-on-one interviews so you can choose the best engineers. And with tools for recording meeting notes, building collaborative meeting agendas, and creating meeting action items, your team can work together on all things cybersecurity.